Apple Is Turning Off iCloud Encryption in the UK
 Credit: Getty Images / Unsplash+
Credit: Getty Images / Unsplash+
Toggle Dark Mode
Rather than complying with an order to build a backdoor into its iCloud encryption, Apple is pulling the plug entirely on its Advanced Data Protection feature for users in the United Kingdom.
Earlier this month, a report from The Washington Post revealed that government security officials in the UK were demanding that Apple provide a backdoor in iCloud that would grant them access to all content stored by users on Apple servers.
To make matters worse, this shadowy order, made under the country’s Investigatory Powers Act, didn’t just apply to Apple customers in the UK. The Home Secretary’s Office insisted that it had the right to demand Apple give it blanket access to data for every iCloud user on the planet. On top of that, it’s also a criminal offense under the Act for Apple to even reveal that it’s received such a demand from the UK government.
Needless to say, US lawmakers were not impressed at the notion of the UK Home Office encroaching on the rights of their citizens and pushed for the newly-minted National Intelligence Director, Tulsi Gabbard, to draw a line in the sand on future intelligence cooperation between the two countries should the UK proceed with its ill-advised plan.
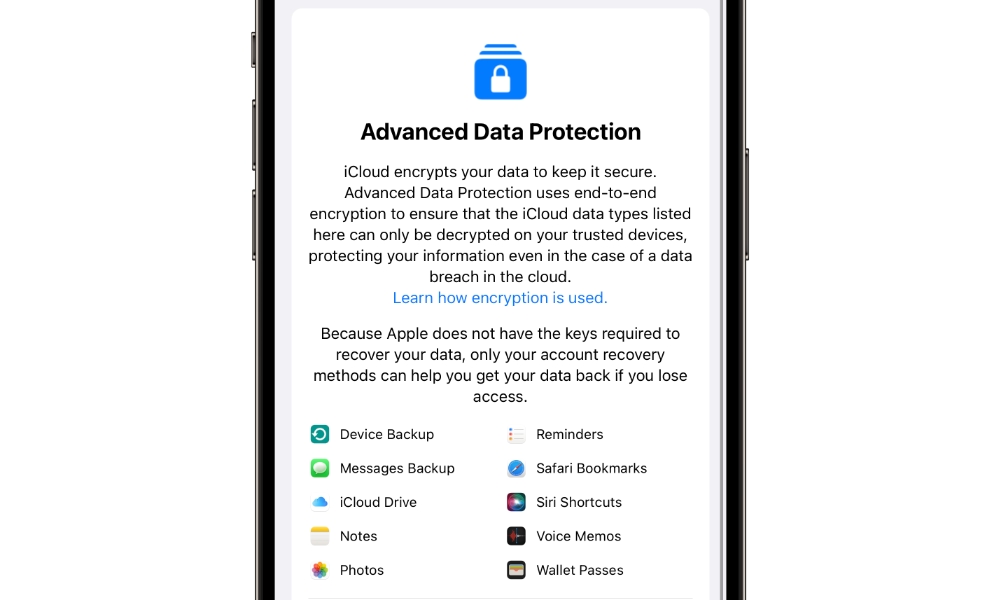
Due to the draconian nature of the UK law, Apple can’t make any public comment about the request. However, it’s tacitly responding by unplugging the entire country from its Advanced Data Protection program, which offers end-to-end encryption for nearly everything stored in iCloud.
Earlier today, Bloomberg’s Mark Gurman was told in a statement by Apple that, effective today, Advanced Data Protection will no longer be available to new users in the UK.
We are gravely disappointed that the protections provided by ADP will not be available to our customers in the UK given the continuing rise of data breaches and other threats to customer privacy. ADP protects iCloud data with end-to-end encryption, which means the data can only be decrypted by the user who owns it, and only on their trusted devices.
Apple
Users attempting to enable ADP in the UK now see a banner that reads, “Apple can no longer offer Advanced Data Protection (ADP) in the United Kingdom to new users.”
Those in the UK who are already using ADP won’t have it turned off automatically — Apple couldn’t do that if it wanted to due to the way that E2EE encryption works, and Apple confirmed that to Gurman.
Instead, folks in the UK using ADP with iCloud will receive “additional guidance” in the coming days or weeks explaining how to disable it manually. There will be an “unspecified grace period” for them to do this, but if they don’t turn it off, they’ll likely lose access to their iCloud accounts at some point.
It’s unclear if this move will satisfy the UK spooks demanding unfettered access to Apple’s customers. Most likely not, as ADP remains available in the rest of the world. Apple is also still using full E2EE for data and communications from other services such as iMessage, FaceTime, passwords, and health data. Messages stored in iCloud have always been end-to-end encrypted, but this data can be compromised if you’re also using iCloud Backups, as the decryption key will be stored in the clear within your backup. ADP protected that by encrypting the iCloud Backup.
Without ADP, UK iCloud users will be left with much of their data accessible to law enforcement and other government officials. Still, at least they won’t be left with a false sense of security by believing their data is encrypted and inaccessible.
Regardless of whether it complies with the UK government’s demands, Apple’s move is as an explicit protest against being ordered to create a backdoor into any of its secure systems. Apple first strongly stated this position in 2016, with CEO Tim Cook likening it to the “software equivalent of cancer” when Apple was being asked by the FBI to provide a way into an iPhone used by the San Bernardino shooter. The FBI eventually got in anyway, but without Apple’s help (they also found nothing useful).
As we have said many times before, we have never built a backdoor or master key to any of our products or services and we never will.
Apple
Since then, Apple has faced down US lawmakers, who insist that iPhone encryption creates a “safe haven for criminals.” Even President Donald Trump accused Apple of “refusing to unlock iPhones used by killers and drug dealers” during his first term in office.
It’s not that Apple doesn’t want to help lawmakers catch criminals. The company has routinely complied with lawful warrants to turn over whatever data it can — including anything stored unencrypted in iCloud. However, it rightly maintains that weakening its encryption technology for law enforcement creates a vulnerability that can be exploited by criminal elements, thereby making every iPhone user on the planet considerably more vulnerable to hacks, spyware, and identity theft.
There’s a strong precedent for this take. In 2019, The New York Times revealed that a powerful hacking tool codenamed “EternalBlue” leaked out of the US National Security Agency (NSA) — one of the most secure agencies on the planet — and “wreaked havoc” when it was used by digital extortionists to launch cyberattacks on businesses and government agencies.
After repeatedly standing up to the US government on its home turf, Apple isn’t about to capitulate in the UK. Apple will undoubtedly continue this fight, and some have speculated that it may have no choice but to pull its services from the UK entirely — a step that the company will undoubtedly be willing to take based on its strong position against weakening security for its users.
“Protecting our users’ privacy and the security of their data is at the very heart of everything we do at Apple,” the company said in response to a similar request by UK officials to open up FaceTime and iMessage encryption in 2023.